[12] X-Pack.Security – Konfiguracja
29 marca 2022Skonfiguruj funkcję X-Pack.Security.
[1] Włącz funkcję X-Pack.Security na wszystkich węzłach Elasticsearch. A także ustaw hasło na węźle głównym Elasticsearch.
[root@vlsr01 ~]# mcedit /etc/elasticsearch/elasticsearch.yml # dodaj na końcu lub zmień ustawienia jeśli istnieją xpack.security.enabled: true xpack.security.transport.ssl.enabled: true [root@vlsr01 ~]# systemctl restart elasticsearch [root@vlsr01 ~]# /usr/share/elasticsearch/bin/elasticsearch-setup-passwords interactive Initiating the setup of passwords for reserved users elastic,apm_system,kibana,kibana_system,logstash_system,beats_system,remote_monitoring_user. You will be prompted to enter passwords as the process progresses. Please confirm that you would like to continue [y/N]y # wpisz hasła Enter password for [elastic]: Reenter password for [elastic]: Enter password for [apm_system]: Reenter password for [apm_system]: Enter password for [kibana_system]: Reenter password for [kibana_system]: Enter password for [logstash_system]: Reenter password for [logstash_system]: Enter password for [beats_system]: Reenter password for [beats_system]: Enter password for [remote_monitoring_user]: Reenter password for [remote_monitoring_user]: Changed password for user [apm_system] Changed password for user [kibana_system] Changed password for user [kibana] Changed password for user [logstash_system] Changed password for user [beats_system] Changed password for user [remote_monitoring_user] Changed password for user [elastic]
[2] Na węźle głównym Elasticsearch w klastrze wygeneruj urząd certyfikacji i certyfikat.
[root@vlsr01 ~]# /usr/share/elasticsearch/bin/elasticsearch-certutil ca This tool assists you in the generation of X.509 certificates and certificate signing requests for use with SSL/TLS in the Elastic stack. The 'ca' mode generates a new 'certificate authority' This will create a new X.509 certificate and private key that can be used to sign certificate when running in 'cert' mode. Use the 'ca-dn' option if you wish to configure the 'distinguished name' of the certificate authority By default the 'ca' mode produces a single PKCS#12 output file which holds: * The CA certificate * The CA's private key If you elect to generate PEM format certificates (the -pem option), then the output will be a zip file containing individual files for the CA certificate and private key # wpisz plik wyjściowy, lub naciśnij [Enter], by zostawić domyślny Please enter the desired output file [elastic-stack-ca.p12]: # Enter # ustaw hasło Enter password for elastic-stack-ca.p12 : # --ca [generuje plik CA] [root@vlsr01 ~]# /usr/share/elasticsearch/bin/elasticsearch-certutil cert --ca elastic-stack-ca.p12 This tool assists you in the generation of X.509 certificates and certificate signing requests for use with SSL/TLS in the Elastic stack. The 'cert' mode generates X.509 certificate and private keys. * By default, this generates a single certificate and key for use on a single instance. * The '-multiple' option will prompt you to enter details for multiple instances and will generate a certificate and key for each one * The '-in' option allows for the certificate generation to be automated by describing the details of each instance in a YAML file * An instance is any piece of the Elastic Stack that requires an SSL certificate. Depending on your configuration, Elasticsearch, Logstash, Kibana, and Beats may all require a certificate and private key. * The minimum required value for each instance is a name. This can simply be the hostname, which will be used as the Common Name of the certificate. A full distinguished name may also be used. * A filename value may be required for each instance. This is necessary when the name would result in an invalid file or directory name. The name provided here is used as the directory name (within the zip) and the prefix for the key and certificate files. The filename is required if you are prompted and the name is not displayed in the prompt. * IP addresses and DNS names are optional. Multiple values can be specified as a comma separated string. If no IP addresses or DNS names are provided, you may disable hostname verification in your SSL configuration. * All certificates generated by this tool will be signed by a certificate authority (CA) unless the --self-signed command line option is specified. The tool can automatically generate a new CA for you, or you can provide your own with the --ca or --ca-cert command line options. By default the 'cert' mode produces a single PKCS#12 output file which holds: * The instance certificate * The private key for the instance certificate * The CA certificate If you specify any of the following options: * -pem (PEM formatted output) * -keep-ca-key (retain generated CA key) * -multiple (generate multiple certificates) * -in (generate certificates from an input file) then the output will be be a zip file containing individual certificate/key files # wpisz hasło wygenerowanego CA Enter password for CA (elastic-stack-ca.p12) : # określ nazwę pliku wyjściowego (jeśli chcesz pozostawić domyślne, naciśnij [Enter]) Please enter the desired output file [elastic-certificates.p12]: # ustaw hasło Enter password for elastic-certificates.p12 : Certificates written to /usr/share/elasticsearch/elastic-certificates.p12 This file should be properly secured as it contains the private key for your instance. This file is a self contained file and can be copied and used 'as is' For each Elastic product that you wish to configure, you should copy this '.p12' file to the relevant configuration directory and then follow the SSL configuration instructions in the product guide. For client applications, you may only need to copy the CA certificate and configure the client to trust this certificate. [root@vlsr01 ~]# chgrp elasticsearch /usr/share/elasticsearch/elastic-certificates.p12 /usr/share/elasticsearch/elastic-stack-ca.p12 [root@vlsr01 ~]# chmod 640 /usr/share/elasticsearch/elastic-certificates.p12 /usr/share/elasticsearch/elastic-stack-ca.p12 [root@vlsr01 ~]# mv /usr/share/elasticsearch/elastic-* /etc/elasticsearch/
[3] Skopiuj CA i certyfikat, które wygenerowałeś powyżej, do wszystkich węzłów Elasticsearch w klastrze. (w tym przykładzie jest pod [/etc/elasticsearch/])
[4] Skonfiguruj X-Pack.Security dla CA i Certyfikatu na wszystkich węzłach Elasticsearch.
# dodaj hasło CA do magazynu kluczy [root@vlsr01 ~]# /usr/share/elasticsearch/bin/elasticsearch-keystore add xpack.security.transport.ssl.keystore.secure_password Enter value for xpack.security.transport.ssl.keystore.secure_password: # dodaj hasło certyfikatu do magazynu kluczy [root@vlsr01 ~]# /usr/share/elasticsearch/bin/elasticsearch-keystore add xpack.security.transport.ssl.truststore.secure_password Enter value for xpack.security.transport.ssl.truststore.secure_password: [root@vlsr01 ~]# mcedit /etc/elasticsearch/elasticsearch.yml # dodaj na końcu xpack.security.transport.ssl.verification_mode: certificate xpack.security.transport.ssl.keystore.path: /etc/elasticsearch/elastic-certificates.p12 xpack.security.transport.ssl.truststore.path: /etc/elasticsearch/elastic-certificates.p12
[5] Ustaw ustawienia SSL, które są używane w połączeniu między serwerem Elasticsearch a klientami.
Musi więc zdobyć certyfikaty SSL (własne certyfikaty lub certyfikaty z Let’s Encrypt).
Środowisko w tym przykładzie zawiera skopiowane certyfikaty, które utworzyliśmy sami, skopiowano je do [/etc/elasticsearch].
[root@vlsr01 ~]# chgrp elasticsearch /etc/elasticsearch/server.* [root@vlsr01 ~]# chmod 640 /etc/elasticsearch/server.* [root@vlsr01 ~]# mcedit /etc/elasticsearch/elasticsearch.yml # dodaj na końcu xpack.security.http.ssl.enabled: true xpack.security.http.ssl.key: /etc/elasticsearch/server.key xpack.security.http.ssl.certificate: /etc/elasticsearch/server.crt [root@vlsr01 ~]# systemctl restart elasticsearch # zweryfikuj dostęp do https: hasło jest tylko tym, które ustawiłeś w sekcji [1] [root@vlsr01 ~]# curl -k https://vlsr01.zicher.lab:9200/_cat/indices?v -u elastic Enter host password for user 'elastic': # wpisz hasło health status index uuid pri rep docs.count docs.deleted store.size pri.store.size green open .apm-agent-configuration 5G3uKQzFReOnbIAS1thWCg 1 0 0 0 226b 226b yellow open packetbeat-7.17.1-2022.03.27-000001 YmtowBRbQjSaYcjWVRqRHA 1 1 1330729 0 414.5mb 414.5mb green open .kibana_task_manager_7.17.1_001 OSLFw2ALSgi4QKmU_ucjOA 1 0 17 539 110.6kb 110.6kb green open .tasks zzQyLMVcSE230Gupspn2lw 1 0 2 0 7.8kb 7.8kb green open .geoip_databases 3Blp2ITzT3OGMcKpXWQmvQ 1 0 44 5 45.5mb 45.5mb green open .security-7 247rR9VcTumzrrviLy0v8Q 1 0 7 0 25.7kb 25.7kb yellow open sshd_fail-2022.03 oEnHEEU5QAe_qnDkUUhxYg 1 1 44 0 58.3kb 58.3kb green open .apm-custom-link xQPmqjYQQNGk7jqY47y5lg 1 0 0 0 226b 226b green open .monitoring-es-7-2022.03.28 z7kf4vveQEu12Tg6Tj3ypA 1 0 6169 2862 5.6mb 5.6mb yellow open metricbeat-7.17.1-2022.03.26-000001 7YefwbdcSdehjGkbWHoFog 1 1 205213 0 130.7mb 130.7mb yellow open heartbeat-7.17.1-2022.03.27-000001 A6XA-CJiSl6FMPlIJr_B_Q 1 1 7232 0 10.1mb 10.1mb green open .async-search KVliO2njSce1JuGEXKxeuQ 1 0 44 16 79.1kb 79.1kb green open .monitoring-kibana-7-2022.03.28 NbAhkdG4Saq-5VG9BthBsg 1 0 126 0 218.5kb 218.5kb green open .kibana_7.17.1_001 rnb6SpMkQQmPFx1PI4t77Q 1 0 6211 666 4.5mb 4.5mb yellow open winlogbeat-7.17.1-2022.03.27-000001 u1ibH9t3Q--uIDiybRcBxQ 1 1 12244 0 9.6mb 9.6mb yellow open auditbeat-7.17.1-2022.03.27-000001 XPANj74qRra926e9n2o60g 1 1 1465870 0 654.2mb 654.2mb yellow open filebeat-7.17.1-2022.03.27-000001 AHMGTS80TmqndW4G6_Qo8w 1 1 6929 0 1.2mb 1.2mb
[6] Jeśli Kibana lub Logstash są uruchomione, skonfiguruj je również dla nich wtyczki Security.
[root@vlsr01 ~]# mcedit /etc/kibana/kibana.yml # linia 32: odkomentuj i zmień na adres https:// elasticsearch.hosts: "https://vlsr01.zicher.lab:9200" # linia 45: odkomentuj i zmień na nazwę użytkownika i hasło ustawione w sekcji [1] elasticsearch.username: "kibana_system" elasticsearch.password: "TajneHasło" [root@vlsr01 ~]# systemctl restart kibana [root@vlsr01 ~]# mcedit /etc/logstash/logstash.yml # dodaj na końcu # wpisz nazwę użytkownika i haslo ustawione w sekcji [1] xpack.monitoring.enabled: true xpack.monitoring.elasticsearch.url: "https://vlsr01.zicher.lab:9200/" xpack.monitoring.elasticsearch.username: "logstash_system" xpack.monitoring.elasticsearch.password: "TajneHasło" xpack.management.enabled: true xpack.management.elasticsearch.url: "https://vlsr01.zicher.lab:9200/" xpack.management.elasticsearch.username: "logstash_system" xpack.management.elasticsearch.password: "TajneHasło" [root@vlsr01 ~]# systemctl restart logstash
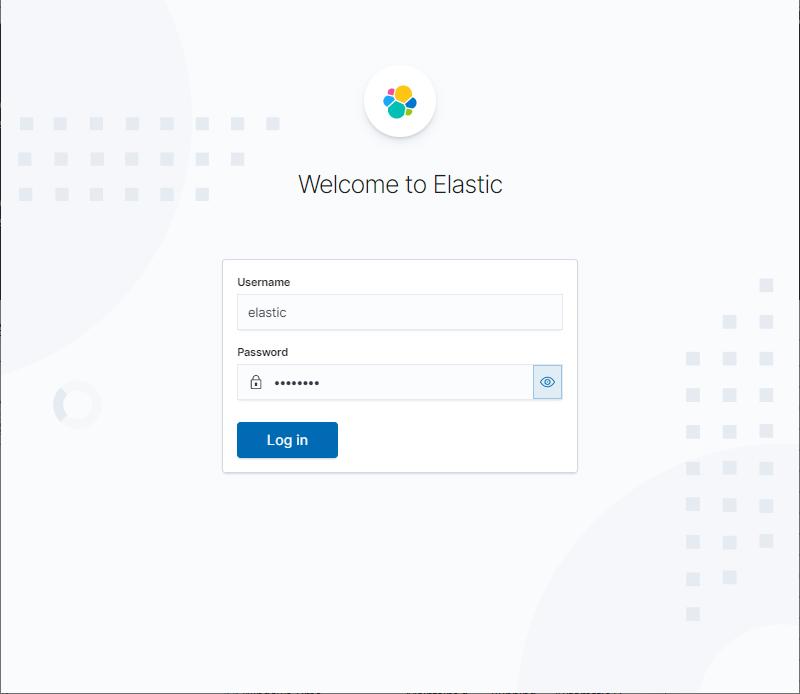
[7] Uzyskaj dostęp do Kibana Dashboard, a następnie wpisz nazwę użytkownika i hasło, które są wymagane. Możesz się z nimi uwierzytelnić, to te, które ustawiłeś w sekcji [1].